The SolarWinds Hack
A Cyber Espionage Nightmare That Shook the World
Hi! 👋 I'm Cicada(my digital name), welcome to my blog!
I’m a Software Engineer based in India.
I have 8+ years of professional experience, 4 of them working with Database, 3 of them as DevOps engineer and 1+ as Automation/ML Eng. Over these years, I’ve been developing and releasing different software and tools.
I write about Machine Learning/AI, but anything related to my area of expertise is a great candidate for a tutorial. I’m interested in Machine Learning/AI and Python.
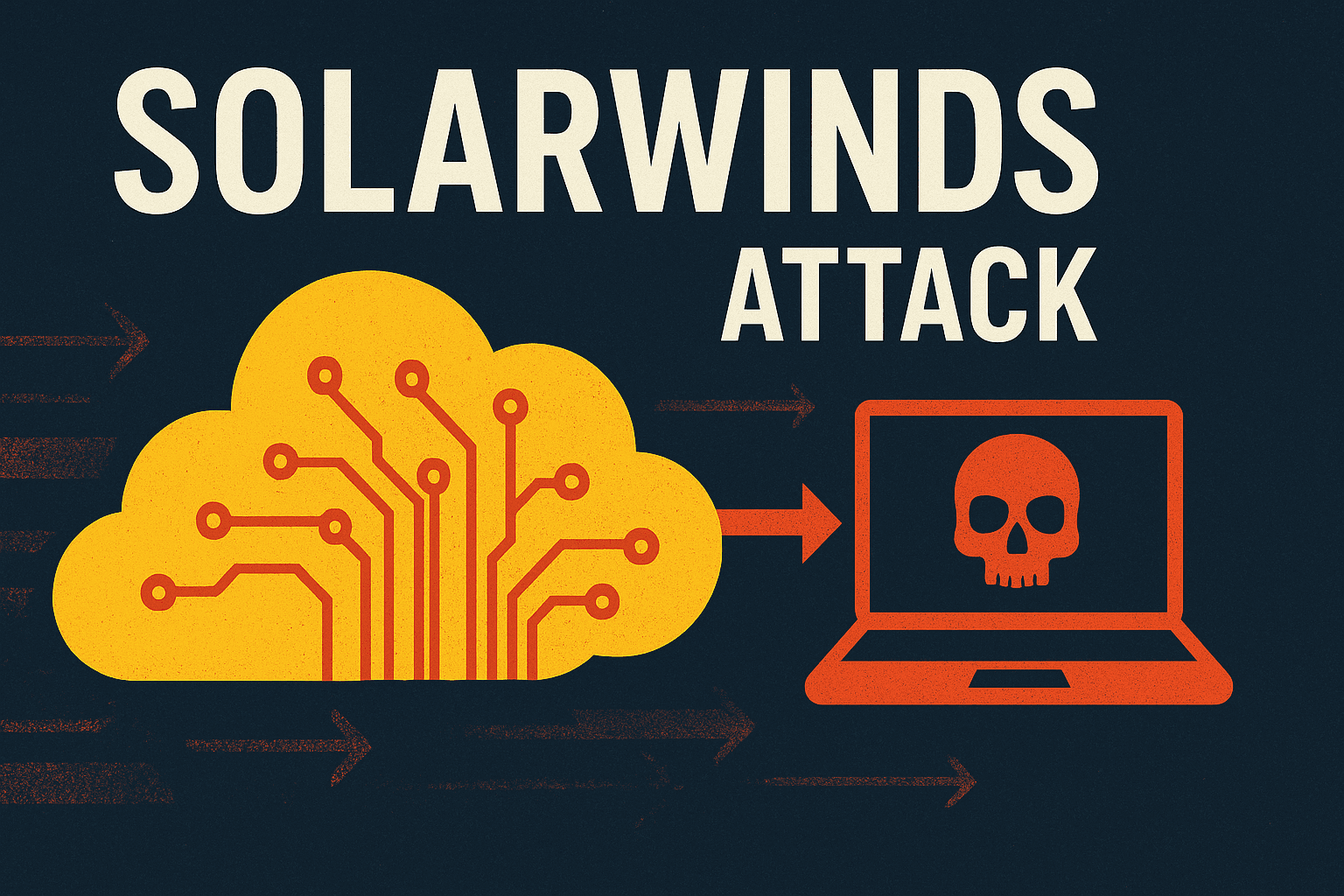
In 2019, the unthinkable happened: one of the largest cyberattacks in history compromised the entire United States government along with some of its biggest corporations. The attack vector? A little-known software company named SolarWinds, whose products quietly managed the IT infrastructure of these powerful institutions. This is the story of how a single supply chain attack cracked open the doors to some of the most secure networks in the world.
A Guard at the White House
Picture this: you’re a security guard at the White House, diligently monitoring security camera feeds. Yet, you’re not just any guard — you are under continuous watch by superiors, as part of a complex security apparatus protecting the President. The entire system is designed to be watertight and foolproof. But what if someone was watching the guards? What if someone had slipped past all the protections, quietly opening a backdoor into the network itself?
This backdoor was real. It gave attackers unrestricted access to the White House network monitoring system for months, enabling them to see everything they wished — unnoticed.
The Breach Beyond the White House
The horrifying reality was that the White House was just one of many victims. This backdoor affected every branch of the US government, the military, and thousands of major companies worldwide. The common factor? SolarWinds software. This attack, now known as one of the most notorious cyber espionage events ever, showed how deeply intertwined modern software supply chains are. The software you rely on often comes via a chain of thousands of companies and contractors — and any weak link compromises the whole chain.
The Complexity of Supply Chains
Think about the phone or computer you’re using now. Its components were crafted in factories run by different companies, built piece by piece by countless subcontractors. The same goes for software — behind every app are layers of software dependencies from various companies.
So what if one link in this intricate chain is infiltrated by attackers? The problem quickly cascades downstream, affecting everyone relying on that product, no matter how secure they try to be.
This is the essence of a supply chain attack — and it’s as insidious as it sounds. In many cyber breaches, the root cause lies far upstream from the final victim.
Why SolarWinds?
SolarWinds, based in Texas, might not be a household name, but it plays an outsized role in enterprise IT. Its software, designed for specialized network management, is used by 425 of the Fortune 500 companies, every major US telecom provider, all branches of the US military, and even the White House itself.
That customer list was a goldmine for attackers — a roadmap into some of the most sensitive networks on Earth.
The Attack Unfolds
Though the exact way attackers initially breached SolarWinds remains unclear, it likely involved zero-day vulnerabilities and carefully crafted phishing campaigns. One plausible scenario involved an employee clicking a legitimate-looking LinkedIn message link that silently exploited a Safari browser bug, stealing credentials.
With these keys in hand, hackers explored SolarWinds’ network over months. Then the real damage began. They targeted SolarWinds’ Orion IT management software. Orion updates were poisoned with a Trojan backdoor, signed and distributed just like any normal update — trusted implicitly by thousands of critical clients.
The Trojan Within: How SUNBURST Worked
his malicious update included a trojanized DLL file that established a hidden communication line to attacker servers. After lying dormant for up to two weeks, it executed commands to transfer files, profile the system, and disable security tools — all while masquerading as legitimate SolarWinds traffic.
If the attacker found the victim valuable, they would deploy further custom malware designed for stealthy espionage or data theft.
Reaching Every Corner
The cleverness of the supply chain attack meant that in one stroke, thousands of networks were infected. Rather than laboriously hacking each target individually, the attackers compromised the update supply channel itself — a singular vulnerability with wide-reaching consequences.
Selective Stealing
Despite the broad infection, the attackers were surgical in what data they stole. From 300,000 SolarWinds customers, about 33,000 installed the compromised Orion updates. Among these, only a few dozen appear to have had sensitive data extracted — mostly among the highest echelons of government like the Department of Defense, NSA, and the White House.
The Discovery
Surprisingly, it wasn’t a government agency that uncovered the breach but FireEye, a cybersecurity contractor. Their engineers traced suspicious activity to SolarWinds software, uncovering the supply chain backdoor. Working fast, FireEye collaborated with Microsoft and others to sinkhole the attackers’ command servers — halting the spread before public awareness even caught up.
The Fallout
The attack, dubbed SUNBURST, quickly became front-page news. SolarWinds’ reputation was shattered as the world learned how one software vendor’s compromise shook the foundations of US cybersecurity.
Criticism mounted over SolarWinds’ lax security and their slow response even after the breach was discovered. Attempts to scapegoat an intern with a weak password were widely ridiculed, missing the point that this was a highly sophisticated nation-state operation.
Who Was Behind It?
Almost unanimously, security agencies and private firms traced the attack back to Russian intelligence operatives, particularly the APT29 group known as Cozy Bear. Their brutal efficiency and suite of advanced tools matched previous espionage campaigns attributed to them.
A Second Wave: Supernova
At the same time as SUNBURST, another attack, Supernova, was discovered — linked to Chinese state-sponsored hackers using different tactics. The attackers exploited the chaos to steal even more credentials from SolarWinds networks.
Conclusion
The SolarWinds hack remains a sobering reminder of the risk posed by supply chain attacks — threats that transcend individual companies and impact entire national security ecosystems. It has galvanized efforts for stronger cybersecurity, improved software supply chain hygiene, and better collaboration between public and private sectors worldwide.