Operation Aurora
A quiet click that shook Google
Hi! 👋 I'm Cicada(my digital name), welcome to my blog!
I’m a Software Engineer based in India.
I have 8+ years of professional experience, 4 of them working with Database, 3 of them as DevOps engineer and 1+ as Automation/ML Eng. Over these years, I’ve been developing and releasing different software and tools.
I write about Machine Learning/AI, but anything related to my area of expertise is a great candidate for a tutorial. I’m interested in Machine Learning/AI and Python.
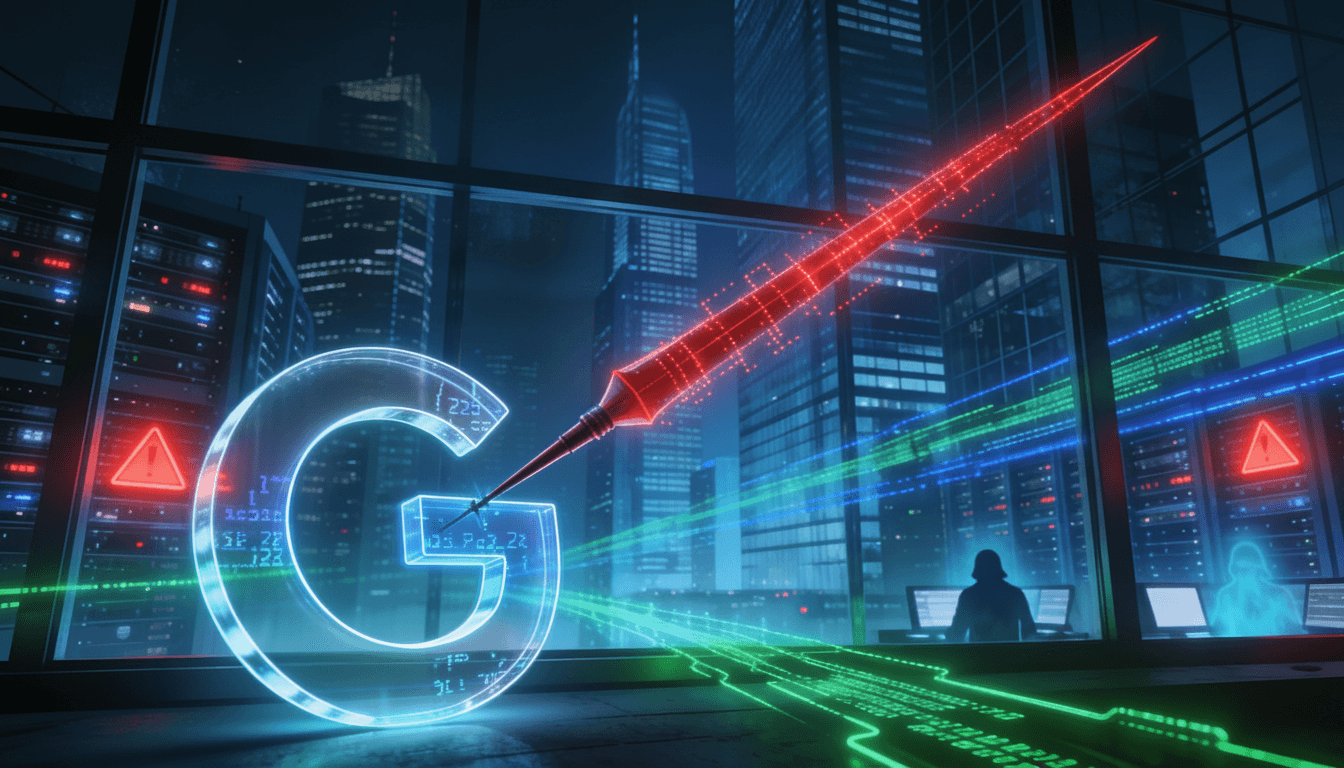
On a quiet day in late 2009, a single careless click inside Google triggered one of the most consequential cyber espionage campaigns in modern history. What started as a routine test in Internet Explorer 6 became the opening move in “Operation Aurora” – a multi‑year, multi‑company hack that rewrote how governments think about cyber power, corporate data, and even war itself.
How one infected page breached Google
The story begins with a Google employee using an old Windows XP machine and Internet Explorer 6 for compatibility testing. An email or IM link led them to a malicious website that silently exploited a zero‑day vulnerability in Internet Explorer, installing a trojan known as Hydraq.
Hydraq downloaded and launched a backdoor DLL, then wiped its own traces so normal monitoring would not notice.
From that point on, the compromised machine kept a constant connection to a command‑and‑control server, ready to execute attacker commands, exfiltrate data, and move laterally.
The attackers then used the victim’s MSN chat account to send more malicious links to colleagues, quickly spreading deeper into Google’s internal network.
Crucially, no amount of “good hygiene” could have fully stopped this first wave – these were genuine zero‑day exploits in mainstream products like Internet Explorer and Adobe’s Flash‑integrated PDF stack.
Zero‑days, Hydraq, and NAID: cyber “nukes”
Hydraq became the public face of Operation Aurora, but it was only part of a tailored toolkit. Security researchers later discovered:
Hydraq actually came in two parts: one trojan to get in, one backdoor to persist.
Development traces suggest work on Hydraq began around 2006 – years before the first detected attacks – highlighting long‑term planning.
A second, more secret backdoor called NAID was reserved for “high value” victims, using a custom communications protocol and stolen digital certificates to blend in as legitimate software.
Zero‑day vulnerabilities – previously unknown, unpatched flaws – are often compared to nuclear weapons in cyberspace: rare, expensive, and usually reserved for state‑level actors. Aurora’s operators didn’t just use one zero‑day; over time they were linked to multiple unique exploits across Internet Explorer and Adobe products.
What the attackers really wanted
The target list reads like a who’s who of global industry: Google, Adobe, Intel, Yahoo, defense contractors like Northrop Grumman, and energy giants such as ExxonMobil and Dow Chemical. Investigations converged on several core objectives.
Source code theft:
Attackers focused on software configuration management systems like Perforce, where entire codebases were accessible to many employees by design.
By compromising just a few lower‑privilege accounts, they could access the “crown jewels” – internal source code – across multiple companies.
The same group later turned up using a disproportionately high number of zero‑days, suggesting they mined stolen code to find fresh vulnerabilities systematically.
Strategic intellectual property:
Targets like ExxonMobil and Dow Chemical held proprietary technology, processes, and market data invaluable to a rapidly industrializing economy.
Gaining access meant accelerating domestic innovation without bearing the full cost of R&D.
Human and political targets:
Attempted access to Gmail accounts linked to dissidents such as artist and activist Ai Weiwei showed clear interest in surveillance of regime critics.
Reports suggest the attackers probed whether US tech firms had received lawful intercept orders related to suspected Chinese spies, and even explored tampering with those wiretapping systems.
This was not random vandalism; it was a broad, coordinated intelligence operation across technology, industry, and human networks.
China’s cyberpunk doctrine and “Shi”
To understand Aurora’s logic, it helps to see it through the language of Chinese information‑warfare theory.
Chinese military and policy thinkers in the 1990s and 2000s wrote extensively about using information warfare to offset US “hegemony.”
A key concept is Shi – strategic advantage gained by knowing the battlefield better than the opponent, ideally to such a degree that victory comes without open conflict.
Those writings extended the idea of “battlefield” from military spaces to everything: politics, economics, culture, and technology. Everyone is a potential adversary, every domain a potential front.
Seen through that lens, global corporations are not neutral businesses but critical terrain: they hold data, code, customers, and leverage. Breaching them becomes a way to accumulate Shi – knowledge and positioning – in a world framed as permanent, total competition.
Tracing Aurora back to China
Attribution in cyberspace is notoriously tricky, but Aurora left behind an unusual number of fingerprints. Individually, each is arguable; collectively, they are hard to dismiss.
Key indicators included:
Code‑level artifacts:
Hydraq contained a specific cyclic redundancy check implementation that was obscure globally but relatively common in Chinese software.
Build paths in the malware revealed a folder named “Aurora Source,” a rare glimpse into how the attackers themselves labeled the operation.
Infrastructure geography:
Early command‑and‑control traffic clustered inside China before steadily reaching Taiwan, the US, and Google HQ in California.
US government analysis later tied parts of the infrastructure to Chinese institutions like Shanghai Jiaotong University and Lanxiang Vocational School, both known for producing military‑aligned talent.
Targeting and intent:
- Focus on Chinese dissidents’ Gmail, interest in wiretap orders against suspected Chinese spies, and systematic theft of strategically useful IP all tightly matched Beijing’s geopolitical priorities.
Over subsequent years, follow‑on operations that reused tooling and infrastructure from Aurora were linked directly to units under the People’s Liberation Army, reinforcing the original attribution.
Google’s breaking point and a new kind of Cold War
Google’s response made Aurora a global story.
In early 2010, the company published a blog post describing:
The discovery of a sophisticated, multi‑company intrusion campaign.
Evidence of targeting Chinese human‑rights activists’ accounts.
A decision to stop censoring search results in China and begin negotiating an exit from the mainland market.
This was not a quiet incident report; it was a public geopolitical statement from one of the world’s largest tech firms. It framed Aurora not just as a security story, but as a symbol of an emerging conflict where code becomes a primary instrument of state power.
Security analyst Dmitri Alperovitch, who helped analyze Hydraq, named the campaign “Operation Aurora” and later argued that it marked the beginning of a new kind of Cold War between China and the West – a conflict whose frontline runs through data centers, developer tools, and cloud platforms instead of tanks and missiles.
From cyberpunk fantasy to national doctrine
Aurora feels strangely true to the original cyberpunk fiction it echoes: misfits turning technology against powerful institutions. The twist is that in this story, the “punks” are not lone hackers but a rising state using punk tactics to challenge an established global order.
China’s leadership once saw the country as an underdog constrained by Western rules and dominance; information warfare offered a way to bend those rules.
Attacks like Aurora, followed by campaigns like Night Dragon and Shady RAT, became stepping stones in building a mature, aggressive cyber apparatus that now routinely targets critical infrastructure worldwide.
What was once subculture aesthetics – neon skylines, dense networks, omnipresent surveillance – is now part of the lived reality of major Chinese cities and the digital systems that surround them.
In that sense, Operation Aurora sits at a turning point: a moment when cyberpunk stopped being just a genre and started to look a lot like state doctrine.
Why Aurora still matters in 2025 and beyond
Fifteen years later, Operation Aurora is not just an old case study – it is a template.
It showed that zero‑day‑powered espionage against private companies is both feasible and strategically valuable.
It demonstrated how deeply national security now depends on corporate security, from SCM permissions to how logs are analyzed.
It normalized the idea that nations will quietly live inside each other’s networks for years, treating codebases, emails, and internal tools as contested terrain.
As critical infrastructure becomes more connected and AI systems increasingly sit on top of proprietary code and data, the logic behind Aurora only grows stronger: whoever owns, understands, or quietly copies the software that runs the world gains a decisive edge.
The unsettling lesson of Operation Aurora is simple: in a world where everything is code, the first shot in a new Cold War might be nothing more than a link, a browser, and a single unremarkable click.